Defending Against Web Application Attacks
Detect & Respond to Threats – From the Data Center to the Cloud
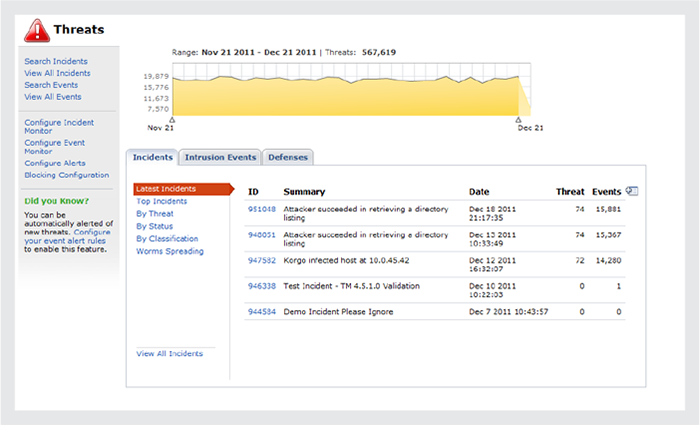
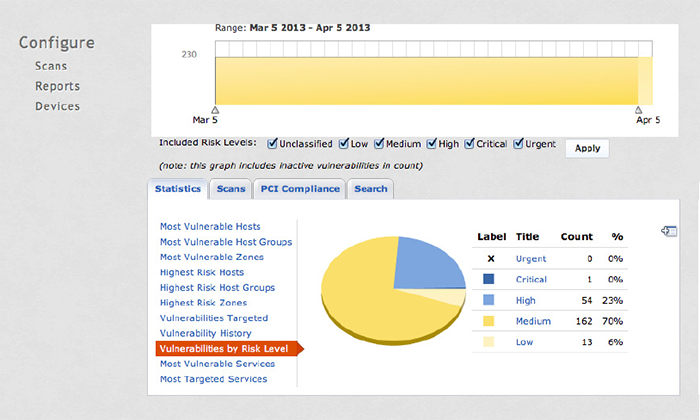
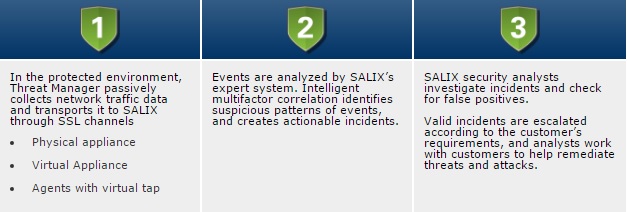
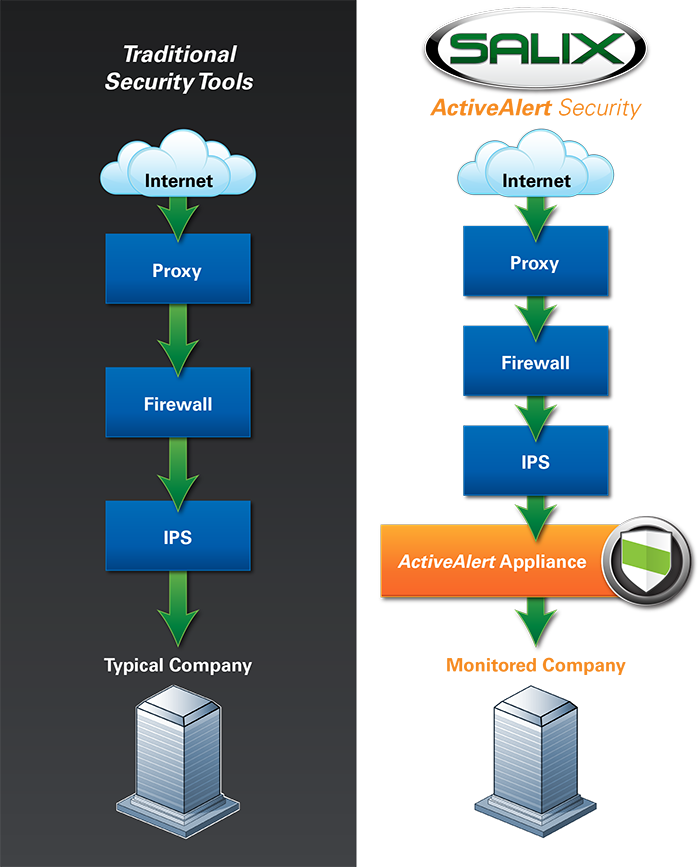
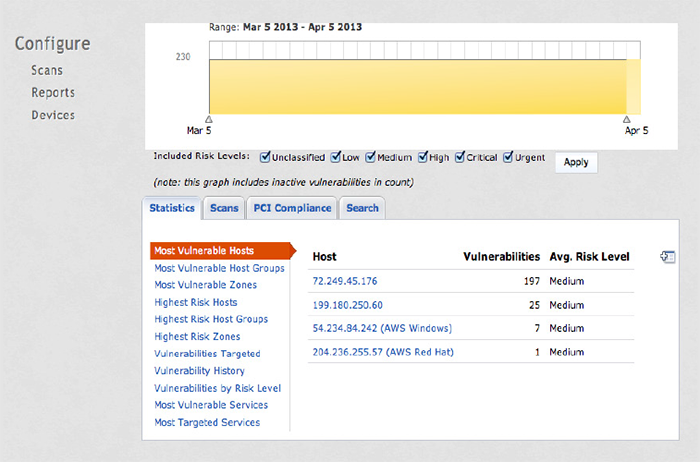
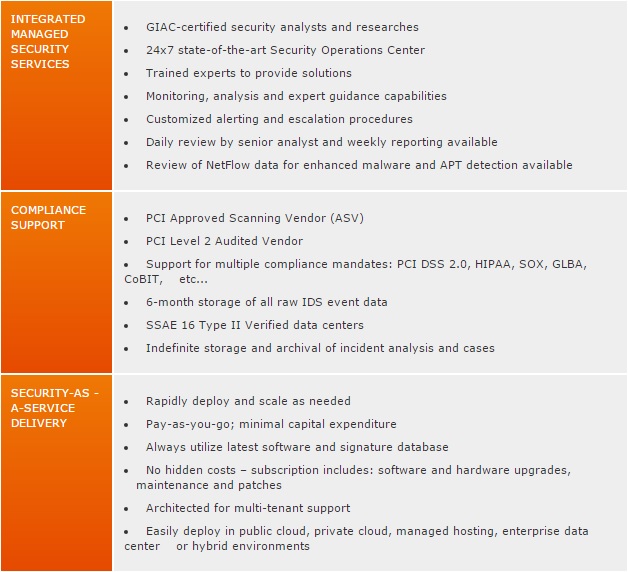
Protecting your infrastructure requires you to detect threats, identify suspicious network traffic, and respond quickly – whether the problem is in your own data center, a hosted environment or the cloud. How do you get a global view of the threats impacting all of your infrastructure, day or night, without massive investments in multiple solutions and additional staff?
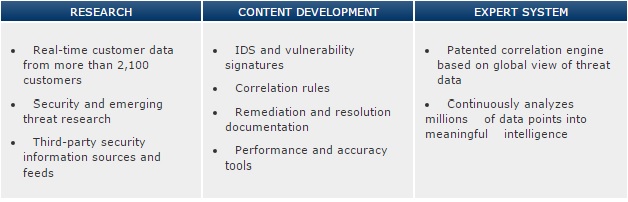
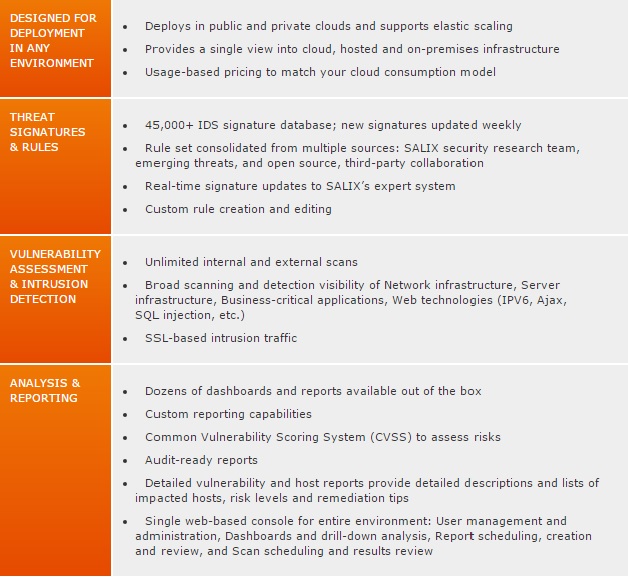
SALIX Threat Manager with ActiveAlert Services gives you 24×7 network threat detection, monitored by SALIX’s Security Operations Center (SOC), for the entire IT environment. Our patented expert system, driven by global threat data, identifies potential problems for our analysts to investigate – acting as an extension of your team, day and night, keeping an eye on suspicious activity.